testssl.sh 是一個用來檢查伺服器 TLS/SSL 安全性的工具,適用於各種有使用加密的網路服務,例如網頁、郵件或 FTP 伺服器等都可以用它來檢測。
伺服器的各種服務加上了 TLS/SSL 之後,可以讓資料以加密的形式在網路上傳輸,確保資料不會被駭客輕易地竊取,不過伺服器的安全性問題並沒有那麼單純,雖然安裝了 TLS/SSL 可以讓伺服器有基本的保護,但後續的設定與維護也非常重要,不當的設定也可能讓伺服器暴露出許多漏洞讓駭客有機可乘。
testssl.sh 是一個開放原始碼的 TLS/SSL 加密安全性檢測工具,可以在 Linux、Mac OS X、FreeBSD 或 MSYS2/Cygwin 等環境中使用,伺服器上各種有使用 TLS/SSL 加密的網路服務(例如網頁、郵件或 FTP 等)都可以用 testssl.sh 來檢測。
Step 1
下載 testssl.sh 指令稿,可以使用 wget 下載:
wget -O testssl.sh testssl.sh
或是用 curl 下載:
curl -L testssl.sh -o testssl.sh
設定 testssl.sh 指令稿的執行權限:
chmod +x testssl.sh
Step 2
使用測試 testssl.sh 測試指定的網站:
./testssl.sh blog.gtwang.org
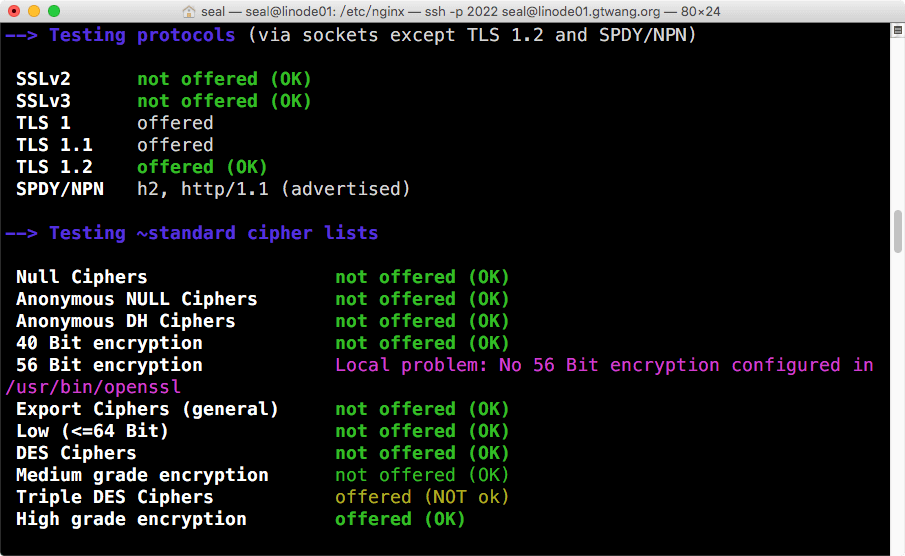
testssl.sh 在執行之後,就會進行各種網站的 TLS/SSL 安全性檢測,而其輸出的報表也非常清楚,沒問題的項目都會以綠色的文字表示。
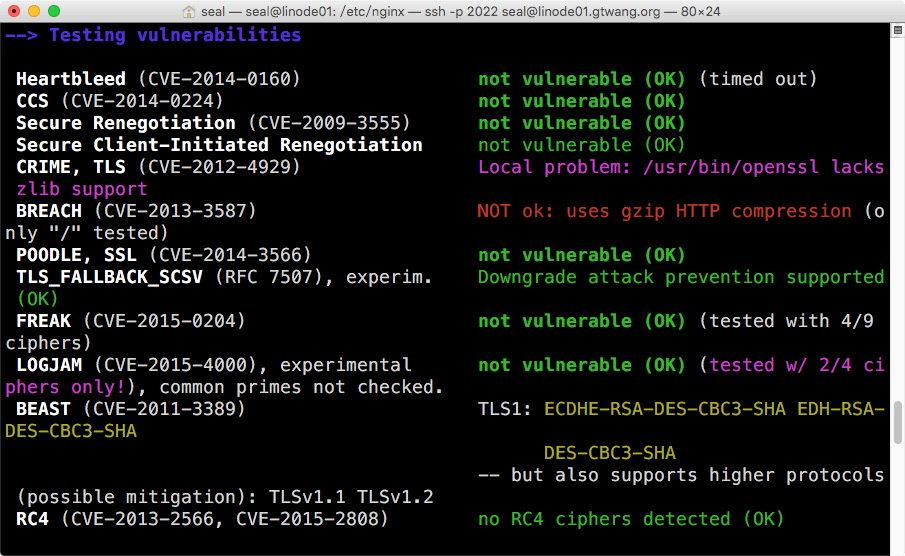
testssl.sh 也會進行各種已知的安全性漏洞檢查,若發現有可能被入侵的弱點時,就會以紅色的文字標示,若您在測試伺服器時出現這樣的紅色訊息,就可以從該弱點的名稱與代號來查詢該如何修正它。
以下是完整的報表內容,給大家參考。
No mapping file found
###########################################################
testssl.sh 2.6 from https://testssl.sh/
(1.379c 2015/09/29 16:47:47)
This program is free software. Distribution and
modification under GPLv2 permitted.
USAGE w/o ANY WARRANTY. USE IT AT YOUR OWN RISK!
Please file bugs @ https://testssl.sh/bugs/
###########################################################
Using "OpenSSL 1.0.1f 6 Jan 2014" [~115 ciphers] on
linode01:/usr/bin/openssl
(built: "May 2 16:53:18 2016", platform: "debian-amd64")
Testing now (2016-05-18 07:22) ---> 45.118.135.69:443 (blog.gtwang.org) <---
further IP addresses: 2400:8901::f03c:91ff:fe67:98b
rDNS (45.118.135.69): li1442-69.members.linode.com. (A record via /etc/hosts)
Service detected: HTTP
--> Testing protocols (via sockets except TLS 1.2 and SPDY/NPN)
SSLv2 not offered (OK)
SSLv3 not offered (OK)
TLS 1 offered
TLS 1.1 offered
TLS 1.2 offered (OK)
SPDY/NPN h2, http/1.1 (advertised)
--> Testing ~standard cipher lists
Null Ciphers not offered (OK)
Anonymous NULL Ciphers not offered (OK)
Anonymous DH Ciphers not offered (OK)
40 Bit encryption not offered (OK)
56 Bit encryption Local problem: No 56 Bit encryption configured in /usr/bin/openssl
Export Ciphers (general) not offered (OK)
Low (<=64 Bit) not offered (OK)
DES Ciphers not offered (OK)
Medium grade encryption not offered (OK)
Triple DES Ciphers offered (NOT ok)
High grade encryption offered (OK)
--> Testing (perfect) forward secrecy, (P)FS -- omitting 3DES, RC4 and Null Encryption here
PFS is offered (OK) ECDHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES256-SHA256 DHE-RSA-AES256-SHA ECDHE-RSA-AES256-SHA384 ECDHE-RSA-AES256-SHA ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES128-SHA256 DHE-RSA-AES128-GCM-SHA256 DHE-RSA-AES128-SHA256 DHE-RSA-AES128-SHA ECDHE-RSA-AES128-SHA
--> Testing server preferences
Has server cipher order? yes (OK)
Negotiated protocol TLSv1.2
Negotiated cipher ECDHE-RSA-AES128-GCM-SHA256
Cipher order
TLSv1: ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA DHE-RSA-AES128-SHA DHE-RSA-AES256-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA AES128-SHA AES256-SHA DES-CBC3-SHA
TLSv1.1: ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA DHE-RSA-AES128-SHA DHE-RSA-AES256-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA AES128-SHA AES256-SHA DES-CBC3-SHA
TLSv1.2: ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES128-GCM-SHA256 DHE-RSA-AES256-GCM-SHA384 ECDHE-RSA-AES128-SHA256 ECDHE-RSA-AES256-SHA384 ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA DHE-RSA-AES128-SHA256 DHE-RSA-AES128-SHA DHE-RSA-AES256-SHA256 DHE-RSA-AES256-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA AES128-GCM-SHA256 AES256-GCM-SHA384 AES128-SHA256 AES256-SHA256 AES128-SHA AES256-SHA DES-CBC3-SHA
h2: ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES128-GCM-SHA256 DHE-RSA-AES256-GCM-SHA384 ECDHE-RSA-AES128-SHA256 ECDHE-RSA-AES256-SHA384 ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA DHE-RSA-AES128-SHA256 DHE-RSA-AES128-SHA DHE-RSA-AES256-SHA256 DHE-RSA-AES256-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA AES128-GCM-SHA256 AES256-GCM-SHA384 AES128-SHA256 AES256-SHA256 AES128-SHA AES256-SHA DES-CBC3-SHA
http/1.1: ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES128-GCM-SHA256 DHE-RSA-AES256-GCM-SHA384 ECDHE-RSA-AES128-SHA256 ECDHE-RSA-AES256-SHA384 ECDHE-RSA-AES128-SHA ECDHE-RSA-AES256-SHA DHE-RSA-AES128-SHA256 DHE-RSA-AES128-SHA DHE-RSA-AES256-SHA256 DHE-RSA-AES256-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA AES128-GCM-SHA256 AES256-GCM-SHA384 AES128-SHA256 AES256-SHA256 AES128-SHA AES256-SHA DES-CBC3-SHA
--> Testing server defaults (Server Hello)
TLS server extensions renegotiation info, EC point formats, session ticket, heartbeat
Session Tickets RFC 5077 300 seconds
Server key size 2048 bit
Signature Algorithm SHA256 with RSA
Fingerprint / Serial SHA1 CDC977139FF3ECC79F7E6B3ECD751F9F42481330 / 0317B5766AC415983F159B227E35DD16C1BB
SHA256 AB052E3C0629FC97F0C8A8CAAA59A6D15586B123472D38EB9CC1764A235E3C0E
Common Name (CN) blog.gtwang.org (works w/o SNI)
subjectAltName (SAN) blog.gtwang.org gtwang.org
Issuer Let's Encrypt Authority X3 (Let's Encrypt from US)
EV cert (experimental) no
Certificate Expiration >= 60 days (2016-05-15 09:59 --> 2016-08-13 09:59 +0800)
# of certificates provided 2
Certificate Revocation List
OCSP URI http://ocsp.int-x3.letsencrypt.org/
OCSP stapling not offered
TLS timestamp random values, no fingerprinting possible
--> Testing HTTP header response @ "/"
HTTP Status Code 200 OK
HTTP clock skew -1 sec from localtime
Strict Transport Security --
Public Key Pinning --
Server banner nginx
Application banner --
Cookie(s) 1 issued: 1/1 secure, 1/1 HttpOnly
Security headers --
Reverse Proxy banner --
--> Testing vulnerabilities
Heartbleed (CVE-2014-0160) not vulnerable (OK) (timed out)
CCS (CVE-2014-0224) not vulnerable (OK)
Secure Renegotiation (CVE-2009-3555) not vulnerable (OK)
Secure Client-Initiated Renegotiation not vulnerable (OK)
CRIME, TLS (CVE-2012-4929) Local problem: /usr/bin/openssl lacks zlib support
BREACH (CVE-2013-3587) NOT ok: uses gzip HTTP compression (only "/" tested)
POODLE, SSL (CVE-2014-3566) not vulnerable (OK)
TLS_FALLBACK_SCSV (RFC 7507), experim. Downgrade attack prevention supported (OK)
FREAK (CVE-2015-0204) not vulnerable (OK) (tested with 4/9 ciphers)
LOGJAM (CVE-2015-4000), experimental not vulnerable (OK) (tested w/ 2/4 ciphers only!), common primes not checked.
BEAST (CVE-2011-3389) TLS1: ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA
DES-CBC3-SHA
-- but also supports higher protocols (possible mitigation): TLSv1.1 TLSv1.2
RC4 (CVE-2013-2566, CVE-2015-2808) no RC4 ciphers detected (OK)
--> Testing all locally available 115 ciphers against the server, ordered by encryption strength
(Your /usr/bin/openssl cannot show DH/ECDH bits)
Hexcode Cipher Suite Name (OpenSSL) KeyExch. Encryption Bits
-------------------------------------------------------------------------
xc030 ECDHE-RSA-AES256-GCM-SHA384 ECDH AESGCM 256
xc028 ECDHE-RSA-AES256-SHA384 ECDH AES 256
xc014 ECDHE-RSA-AES256-SHA ECDH AES 256
x9f DHE-RSA-AES256-GCM-SHA384 DH AESGCM 256
x6b DHE-RSA-AES256-SHA256 DH AES 256
x39 DHE-RSA-AES256-SHA DH AES 256
x9d AES256-GCM-SHA384 RSA AESGCM 256
x3d AES256-SHA256 RSA AES 256
x35 AES256-SHA RSA AES 256
xc012 ECDHE-RSA-DES-CBC3-SHA ECDH 3DES 168
x16 EDH-RSA-DES-CBC3-SHA DH 3DES 168
x0a DES-CBC3-SHA RSA 3DES 168
xc02f ECDHE-RSA-AES128-GCM-SHA256 ECDH AESGCM 128
xc027 ECDHE-RSA-AES128-SHA256 ECDH AES 128
xc013 ECDHE-RSA-AES128-SHA ECDH AES 128
x9e DHE-RSA-AES128-GCM-SHA256 DH AESGCM 128
x67 DHE-RSA-AES128-SHA256 DH AES 128
x33 DHE-RSA-AES128-SHA DH AES 128
x9c AES128-GCM-SHA256 RSA AESGCM 128
x3c AES128-SHA256 RSA AES 128
x2f AES128-SHA RSA AES 128
Done now (2016-05-18 07:22) ---> 45.118.135.69:443 (blog.gtwang.org) <---除了 testssl.sh 這個工具之外,Qualys 的 SSL Server Test 也是一個可以檢測伺服器 SSL 安全性的工具。如果想要改善伺服器的 TLS/SSL 安全性設定,可以參考 Raymii.org 的文章。
