hostapd 服務
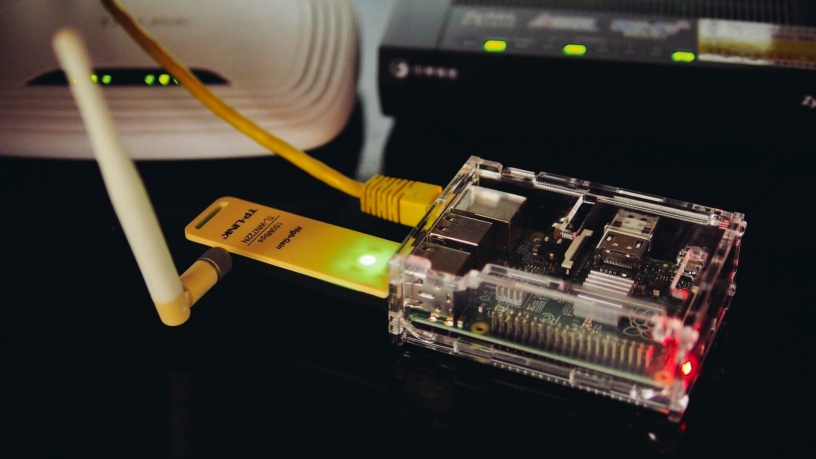
要藉由 USB 無線網路卡建立一個 AP(access point),還需要安裝 hostapd 這個 daemon。
安裝 hostapd:
sudo apt-get install hostapd
建立 /etc/hostapd/hostapd.conf 設定檔,我們可以從 /usr/share/doc/hostapd/examples/hostapd.conf.gz 這個範例檔開始修改。
interface 設定為 wlan0:
# AP netdevice name (without 'ap' postfix, i.e., wlan0 uses wlan0ap for # management frames); ath0 for madwifi interface=wlan0
設定 driver:
# Driver interface type (hostap/wired/madwifi/test/none/nl80211/bsd); # default: hostap). nl80211 is used with all Linux mac80211 drivers. # Use driver=none if building hostapd as a standalone RADIUS server that does # not control any wireless/wired driver. driver=nl80211
設定無線網路的 SSID:
# SSID to be used in IEEE 802.11 management frames
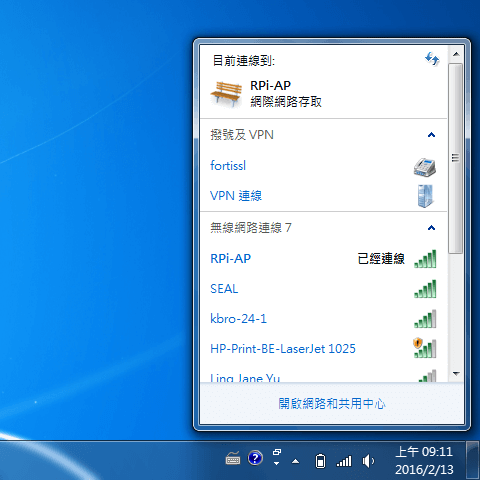
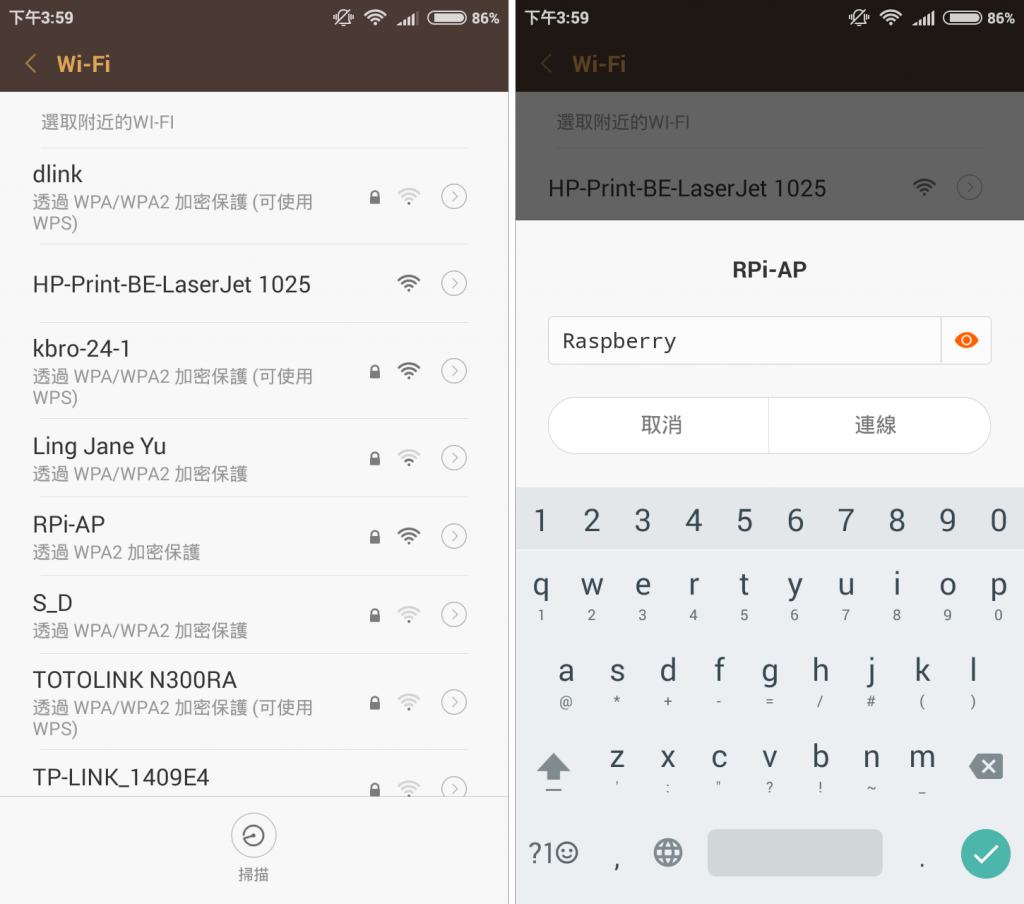
ssid=RPi-AP
無線網路連線模式:
# Operation mode (a = IEEE 802.11a, b = IEEE 802.11b, g = IEEE 802.11g, # ad = IEEE 802.11ad (60 GHz); a/g options are used with IEEE 802.11n, too, to # specify band) # Default: IEEE 802.11b hw_mode=g
無線網路頻道:
# Channel number (IEEE 802.11) # (default: 0, i.e., not set) # Please note that some drivers do not use this value from hostapd and the # channel will need to be configured separately with iwconfig. # # If CONFIG_ACS build option is enabled, the channel can be selected # automatically at run time by setting channel=acs_survey or channel=0, both of # which will enable the ACS survey based algorithm. channel=1
MAC 卡號認證機制設定:
# Station MAC address -based authentication # Please note that this kind of access control requires a driver that uses # hostapd to take care of management frame processing and as such, this can be # used with driver=hostap or driver=nl80211, but not with driver=madwifi. # 0 = accept unless in deny list # 1 = deny unless in accept list # 2 = use external RADIUS server (accept/deny lists are searched first) macaddr_acl=0
無線網路認證演算法設定:
# IEEE 802.11 specifies two authentication algorithms. hostapd can be # configured to allow both of these or only one. Open system authentication # should be used with IEEE 802.1X. # Bit fields of allowed authentication algorithms: # bit 0 = Open System Authentication # bit 1 = Shared Key Authentication (requires WEP) auth_algs=3
# Send empty SSID in beacons and ignore probe request frames that do not # specify full SSID, i.e., require stations to know SSID. # default: disabled (0) # 1 = send empty (length=0) SSID in beacon and ignore probe request for # broadcast SSID # 2 = clear SSID (ASCII 0), but keep the original length (this may be required # with some clients that do not support empty SSID) and ignore probe # requests for broadcast SSID ignore_broadcast_ssid=0
WPA 設定:
# Enable WPA. Setting this variable configures the AP to require WPA (either # WPA-PSK or WPA-RADIUS/EAP based on other configuration). For WPA-PSK, either # wpa_psk or wpa_passphrase must be set and wpa_key_mgmt must include WPA-PSK. # Instead of wpa_psk / wpa_passphrase, wpa_psk_radius might suffice. # For WPA-RADIUS/EAP, ieee8021x must be set (but without dynamic WEP keys), # RADIUS authentication server must be configured, and WPA-EAP must be included # in wpa_key_mgmt. # This field is a bit field that can be used to enable WPA (IEEE 802.11i/D3.0) # and/or WPA2 (full IEEE 802.11i/RSN): # bit0 = WPA # bit1 = IEEE 802.11i/RSN (WPA2) (dot11RSNAEnabled) wpa=2
設定無線網路的密碼:
# WPA pre-shared keys for WPA-PSK. This can be either entered as a 256-bit # secret in hex format (64 hex digits), wpa_psk, or as an ASCII passphrase # (8..63 characters) that will be converted to PSK. This conversion uses SSID # so the PSK changes when ASCII passphrase is used and the SSID is changed. # wpa_psk (dot11RSNAConfigPSKValue) # wpa_passphrase (dot11RSNAConfigPSKPassPhrase) #wpa_psk=0123456789abcdef0123456789abcdef0123456789abcdef0123456789abcdef wpa_passphrase=Raspberry
接受的金鑰管理方式:
# Set of accepted key management algorithms (WPA-PSK, WPA-EAP, or both). The # entries are separated with a space. WPA-PSK-SHA256 and WPA-EAP-SHA256 can be # added to enable SHA256-based stronger algorithms. # (dot11RSNAConfigAuthenticationSuitesTable) #wpa_key_mgmt=WPA-PSK WPA-EAP wpa_key_mgmt=WPA-PSK
# Set of accepted cipher suites (encryption algorithms) for pairwise keys # (unicast packets). This is a space separated list of algorithms: # CCMP = AES in Counter mode with CBC-MAC [RFC 3610, IEEE 802.11i/D7.0] # TKIP = Temporal Key Integrity Protocol [IEEE 802.11i/D7.0] # Group cipher suite (encryption algorithm for broadcast and multicast frames) # is automatically selected based on this configuration. If only CCMP is # allowed as the pairwise cipher, group cipher will also be CCMP. Otherwise, # TKIP will be used as the group cipher. # (dot11RSNAConfigPairwiseCiphersTable) # Pairwise cipher for WPA (v1) (default: TKIP) #wpa_pairwise=TKIP CCMP wpa_pairwise=TKIP # Pairwise cipher for RSN/WPA2 (default: use wpa_pairwise value) rsn_pairwise=CCMP
編輯 /etc/default/hostapd 設定檔,設定 DAEMON_CONF 指向 /etc/hostapd/hostapd.conf:
# Uncomment and set DAEMON_CONF to the absolute path of a hostapd configuration # file and hostapd will be started during system boot. An example configuration # file can be found at /usr/share/doc/hostapd/examples/hostapd.conf.gz DAEMON_CONF="/etc/hostapd/hostapd.conf"
測試一下 hostapd 的設定是否正確,使用 root 管理者權限執行 hostapd,並指定設定檔:
sudo hostapd /etc/hostapd/hostapd.conf
檢查輸出是否有問題,正常來說會類似這樣:
Configuration file: /etc/hostapd/hostapd.conf Using interface wlan0 with hwaddr f8:1a:67:18:3a:ab and ssid "RPi-AP" wlan0: interface state UNINITIALIZED->ENABLED wlan0: AP-ENABLED wlan0: STA 28:e3:1f:50:b9:94 IEEE 802.11: authenticated wlan0: STA 28:e3:1f:50:b9:94 IEEE 802.11: associated (aid 1) wlan0: AP-STA-CONNECTED 28:e3:1f:50:b9:94 wlan0: STA 28:e3:1f:50:b9:94 RADIUS: starting accounting session 56BD92F6-00000000 wlan0: STA 28:e3:1f:50:b9:94 WPA: pairwise key handshake completed (RSN)
無如果正常的話,這時候就可以使用新的無線網路 RPi-AP 了。
一般手機或平板也可以直接使用。
確定設定無誤之後,可以中斷自己執行的 hostapd,將系統的 hostapd 服務:
sudo service hostapd restart
問題檢查
如果在設定上有問題,無法使用的話,可以用 iw 指令檢查一下自己的 USB 無線網路卡是否支援 AP 模式:
iw list
在輸出中找到 Supported interface modes 這一段:
Supported interface modes: * IBSS * managed * AP * AP/VLAN * monitor * mesh point * P2P-client * P2P-GO
確認網路卡有支援 AP 模式。
另外若是軟體設定有問題,除了在終端機上的錯誤訊息之外,在 /var/log/syslog 紀錄檔中也可以找到一些資訊。
參考資料:adafruit、adafruit、maketecheasier、superuser、superuser、Ubuntu Help
繼續閱讀: 12

EricZhang
請問一下 我在
service isc-dhcp-server restart
出現failed to restart isc-dhcp-server.service:access denied
的錯誤 請問是什麼意思?
G. T. Wang
有用 root 權限執行嗎?
EricZhang
不好意思 該怎麼設定root權限 因為我是照這篇教學 練習設定
EricZhang
我有找到資料 使用sudo passwd root 去設定
但是當我使用sudo passwd -u root 時出現
passwd password expiry information changed
EricZhang
我剛剛重新跑一次教學 發現到
# On what interfaces should the DHCP server (dhcpd) serve DHCP requests?
# Separate multiple interfaces with spaces, e.g. “eth0 eth1”.
INTERFACES=”wlan0″
這個設定 您的有#on……這類的註解
但我的是空白頁面 只有我自己輸入的INTERFACES=”wlan0″
是不是我的/etc/default/isc-dhcp-server設定檔有問題 缺少了什麼導致無法start
是不是我的
EricZhang
我剛剛重新將rpi重新安裝後 發現問題源頭
我在spt-get那邊就錯誤了
正在預先設定套件 …
選取了原先未選的套件 isc-dhcp-server。
(讀取資料庫 … 目前共安裝了 125576 個檔案和目錄。)
Preparing to unpack …/isc-dhcp-server_4.3.1-6+deb8u2_armhf.deb …
Unpacking isc-dhcp-server (4.3.1-6+deb8u2) …
Processing triggers for man-db (2.7.0.2-5) …
Processing triggers for systemd (215-17+deb8u4) …
設定 isc-dhcp-server (4.3.1-6+deb8u2) …
–>Generating /etc/default/isc-dhcp-server…
Job for isc-dhcp-server.service failed. See ‘systemctl status isc-dhcp-server.service’ and ‘journalctl -xn’ for details.
invoke-rc.d: initscript isc-dhcp-server, action “start” failed.
Processing triggers for systemd (215-17+deb8u4) …
想請問是什麼原因嗎 我試過用sudo su root 安裝也一樣
ANDY
編輯 /etc/dhcp/dhcpd.conf 設定檔,將 domain name 的全域設定拿掉:
# option definitions common to all supported networks…
# option domain-name “example.org”;
# option domain-name-servers ns1.example.org, ns2.example.org;
請問只要改成這樣而已嗎
# option definitions common to all supported networks…
option domain-name “example.org”;
# option domain-name-servers ns1.example.org, ns2.example.org;
ANDY
請問這段要加在哪呢~?
subnet 192.168.2.0 netmask 255.255.255.0 {
range 192.168.2.10 192.168.2.50;
option broadcast-address 192.168.2.255;
option routers 192.168.2.1;
default-lease-time 600;
max-lease-time 7200;
option domain-name “local”;
option domain-name-servers 168.95.192.1, 168.95.1.1;
}
ANDY
挖!!
我成功了
感謝大大~
請問可以用甚麼方式聯絡您嗎?
G. T. Wang
如果是技術問題,可直接在這裡與我討論,非技術的私人問題,可寄信至我的 Email 信箱。
ANDY
請問您的做法應該是會讓
內部有網路 ,
但是顯示不了網頁 吃不到wifi嗎?
G. T. Wang
抱歉,這裡的網路設定我沒有寫得很清楚。
這裡的做法是用 wlan0 對內提供無線網路,而 eth0 對外連上網際網路,正常來說設定好之後是可以正常上網的。
當然網路的設定有很多方式,這只是常用設定的其中一種。
John Huang
謝謝你的分享
蠻希望 RaspberryPi 之後也能支援 5GHz 的頻段
zetacat
請問:
開啟hostapd時,出現
rfkill: Cannot open RFKILL control device
nl80211: Could not re-add multicast membership for vendor events: -2 (No such file or directory)
是甚麼出錯?如何解決?
目前狀況是手機偵測的到AP但顯示不需要密碼
但我有設wpa_passphrase
而且連的時候一直卡在obtaining ip address
求解惑,感激不盡~
zetacat
#備註 我是使用orangepi ubuntu 16.04.2LTS 而非raspberrypi
maxhu
您好,關於這篇網誌受益匪淺
但想請教,當我們設定好 網路轉發 wifi ap mode,要如何變回來?
不曉得有什麼文章或關鍵字可以參考
Roger Sung
感谢分享
sj
my error message, pls help..
root@orangepizero:~# sudo hostapd /etc/hostapd/hostapd.conf
Configuration file: /etc/hostapd/hostapd.conf
nl80211: Could not configure driver mode
nl80211: deinit ifname=wlan0 disabled_11b_rates=0
nl80211 driver initialization failed.
wlan0: interface state UNINITIALIZED->DISABLED
wlan0: AP-DISABLED
hostapd_free_hapd_data: Interface wlan0 wasn’t started
sj
dnsmasq and isc-dhcp-serve, 哪個好?
sj
請問重開機,要如何自動啟動